BUILT FOR COMPLIANCE
EU AI Act ready. Regulatory-grade provenance.
Voice agents in regulated markets need embedded provenance, auditable logs, and tamper-resistant authentication. Resemble provides the infrastructure out of the box.
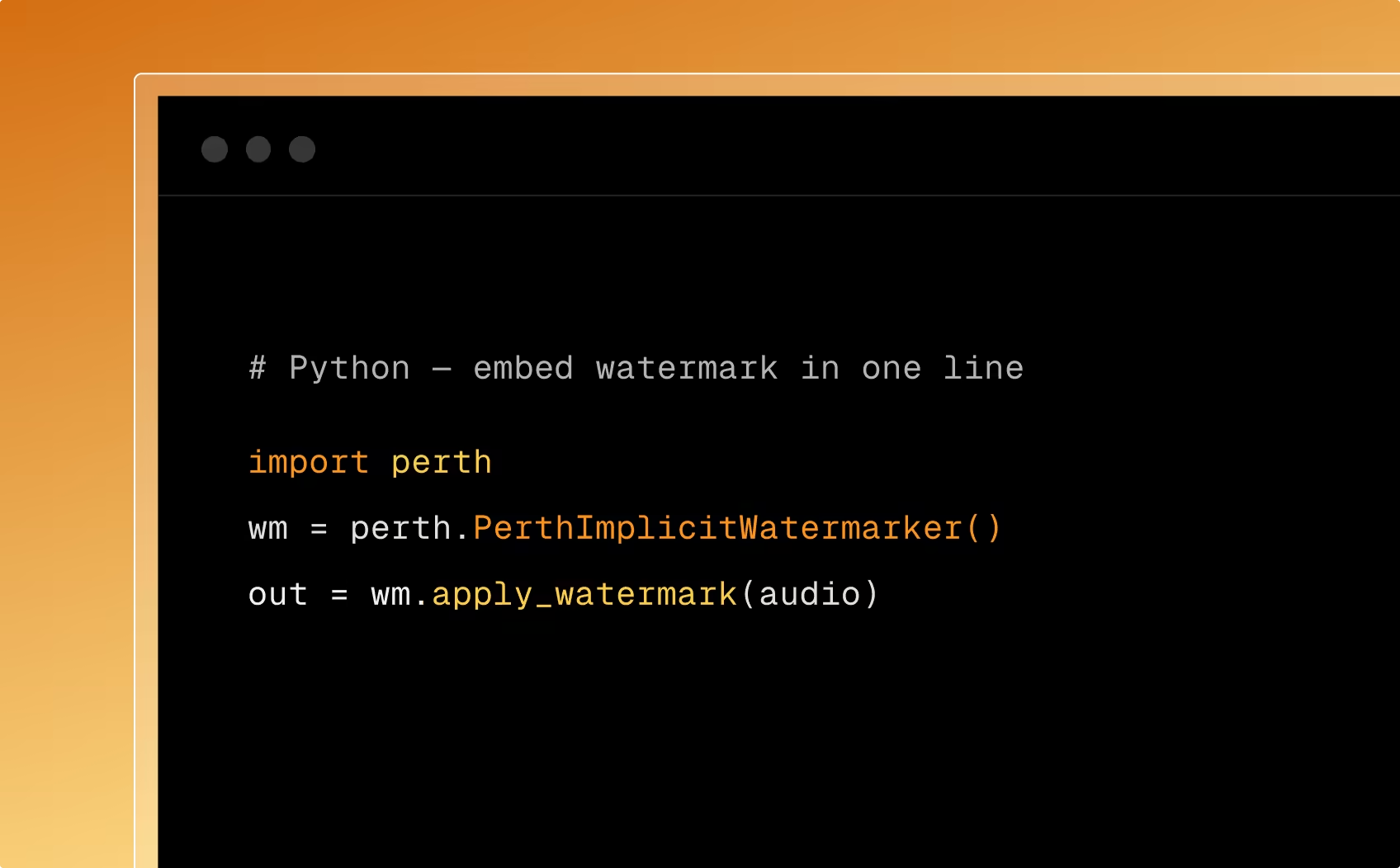
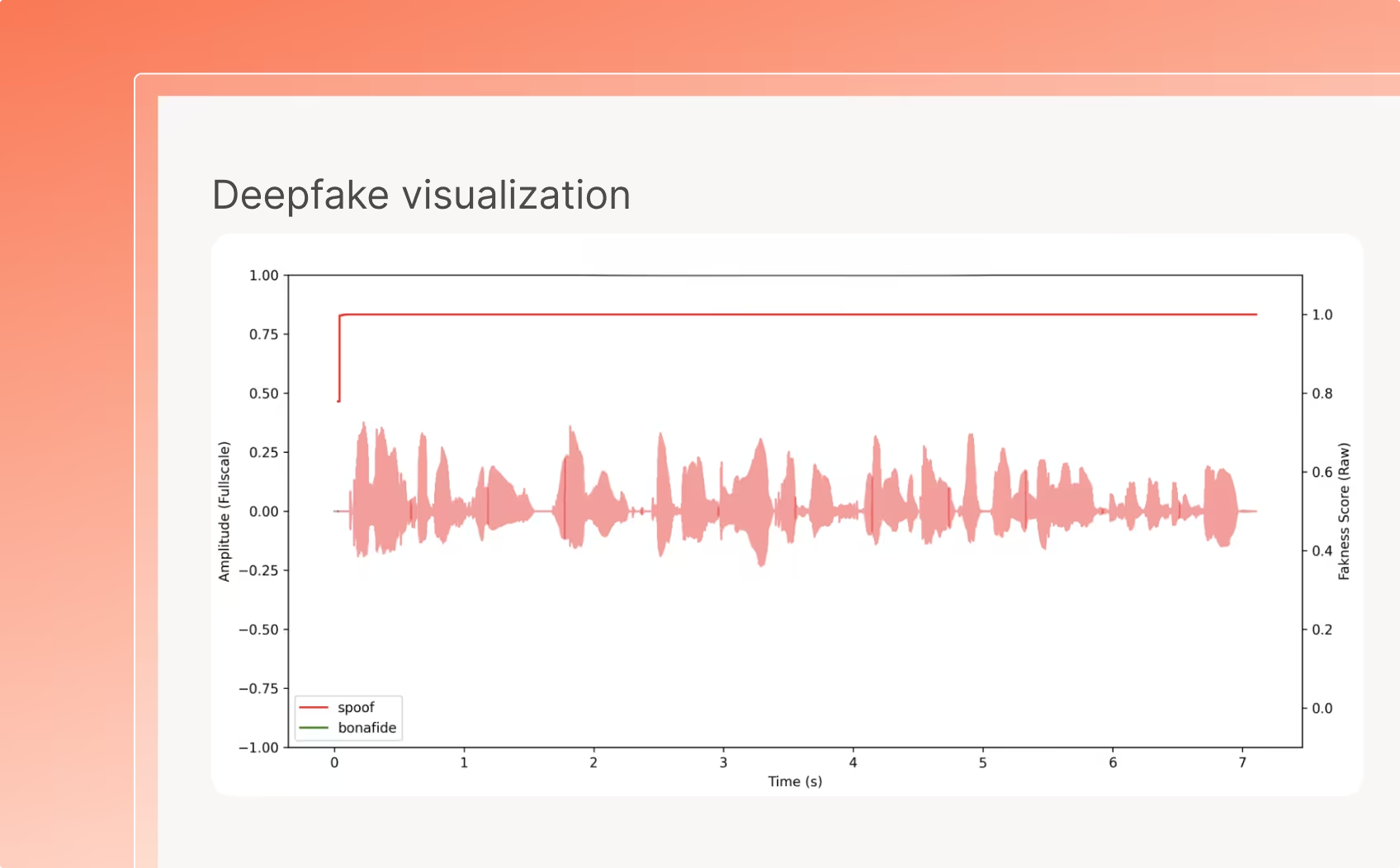
PerTh watermarking provides mandatory AI content identification. Enforcement begins August 2026.
Content traceability and origin verification for synthetic media with auditable provenance chains.
C2PA / Content Provenance
Compatible with emerging content authenticity standards for cross-platform verification.
SOC 2 / Enterprise Security
On-premise deployment, data residency controls, and audit logging for regulated industries.